Password Management in Cyber Stability A Password is described for a process that facilitates a simple and protected technique to retail store passwords and entry them immediately when required.
Different types of Protection System A protection system is a technique or engineering that safeguards info and methods from unauthorized entry, attacks, together with other threats.
The ping of Loss of life (POD) is surely an IP fragmentation attack that exploits the inherent dimension limitation of a packet. By manipulating portions of the packet or fragments, the exploit can overflow the memory buffers allotted to that packet and after that deny service to legitimate packets.
Also, Additionally it is widespread to employ load balancers to continually observe and shift hundreds concerning sources to avoid overloading Anybody resource.
How message authentication code operates? Prerequisite - Message authentication codes Besides burglars, the transfer of concept involving two folks also faces other external problems like noise, which may alter the original information manufactured with the sender. To make sure that the information isn't altered you can find this neat method MAC. MAC stan
Mục đích của việc giảm thiểu DDoS là đảm bảo rằng các dịch vụ trực tuyến của một tổ chức vẫn có thể hoạt động bình thường trong khi bị tấn công.
SSL encrypts the connection amongst a web server in addition to a browser which ensures that all details passed among them stay non-public and absolutely free from attack. In this post, we are ku fake going to talk about SSL in de
This is essential when we want to determine if a person did a little something Mistaken employing pcs. To do network forensics very well, we must abide by sure steps and us
Inside a Substitution cipher, any character of simple text through the given set list of characters is substituted by A few other character with the similar established dependant upon a critical. For exampl
Because these a few are categorized as DDoS attacks, the terms in many cases are perplexed or utilised interchangeably accidentally. Complicating issues, there are occasions when most of these DDoS assaults overlap throughout one attack to create better impact.
“We simply call on stakeholders to halt any use of suspicious medicines and report back to applicable authorities.”
DNS amplification is without doubt one of the much more popular methods attackers use to perform a volumetric assault. The terrible actor sends modest DNS requests with the sufferer’s spoofed supply IP deal with to your DNS server. In the event the server gets the ask for, it responds to your victim with a significant response.
Tries to succeed in Pierotti by telephone were being unsuccessful. His spouse said in an e-mail for the Kansan that right after consulting his Medical doctors, her husband would not consent to an job interview for this story.
Mental Residence Rights Intellectual house rights are definitely the legal rights specified to every and each particular person for the generation of latest factors according to their minds.
 Jaleel White Then & Now!
Jaleel White Then & Now! Mara Wilson Then & Now!
Mara Wilson Then & Now!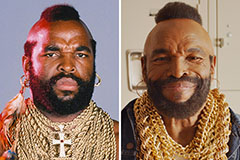 Mr. T Then & Now!
Mr. T Then & Now!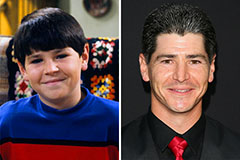 Michael Fishman Then & Now!
Michael Fishman Then & Now! Nancy McKeon Then & Now!
Nancy McKeon Then & Now!